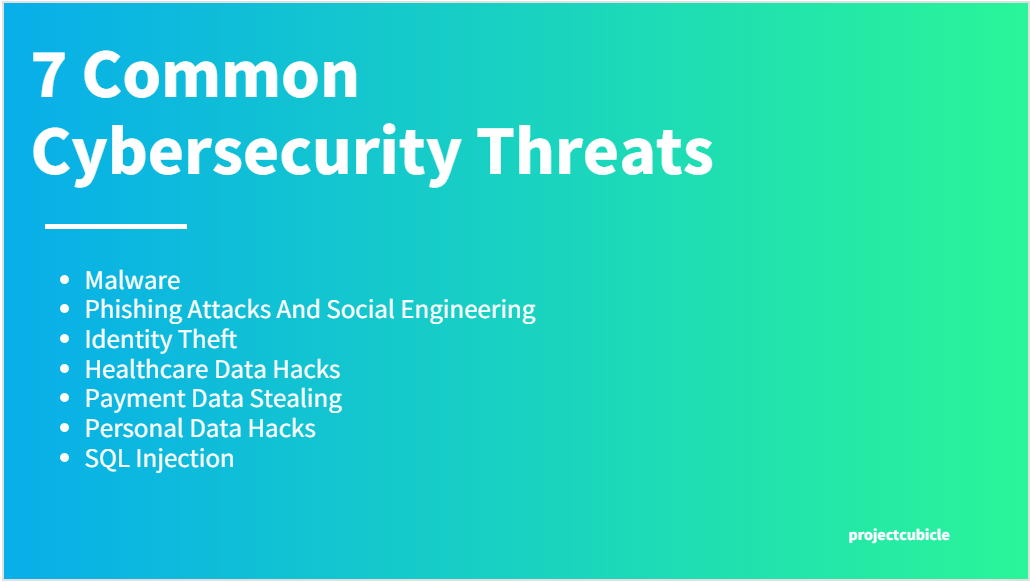
7 Common Cybersecurity Threats We Are Exposed To
We can never deny the blessings of the internet. It has made our life a lot easier and also simpler. The internet has connected the entire world and has developed a connection between every corner of the world. We do not only watch unlimited movies by downloading them from the pirate bay through the internet; we are now doing everything. Whether it is working from home, online, meeting, online classes, online shopping, online transactions, or online payments. Yet, cybersecurity threats are coming from everywhere too. This situation makes cybersecurity threat intelligence and ways to combat cybersecurity threats a quite hot topic.
Table of Contents
Common Cybersecurity Threats That The Average Internet User Is Exposed To
Everything comes with its negative signs. The online world is full of several types of threats. Whether it is malware attacks, phishing attacks, or stealing private information, there is always a risk.
Here, we will talk about some of the common cybersecurity threats that, as an average user, you are always exposed to.
1. Malware
Malware threats or cybersecurity threats are really a common one to get when you are using the internet. You will not know when you will end up getting malware from the game you have downloaded or the new signs you have just got.
This is why it is better to download any game, applications, songs, movies, or even your necessary content only from reputed and trustworthy platforms.
2. Phishing Attacks And Social Engineering
Phishing attacks or social engineering are some new-age cybersecurity threats we all face. You might have heard that whenever you are receiving any media file or attachment through your email, you first must scan that and then download it.
There are several cybercriminals who will force you to download files by sending them to your email. You should be really careful about this kind of cybersecurity threats.
3. Identity Theft
Identity theft is a serious one. Data breaches and phishing emails are some of the most common ways of identity theft. Your email address, social media photos, resume, home address, and financial details are exposed to these types of identity theft risks.
Identity thieves might steal your personal data, such as credit card details, and use them for their evil purposes. So, before exposing your details on social media and any online platform, make sure you are maintaining all the safety precautions.
4. Healthcare Data Hacks
At present, we are using online solutions for almost everything and anything. When it comes to healthcare and medication, we are also utilizing the perks of online solutions. By healthcare data hacks, we mean stealing data from the healthcare system.
There are instances when the cybercriminals have hacked healthcare portals, and after that, have stolen the data of thousands of patients.
5. Payment Data Stealing
As we have mentioned above, we are now looking for online solutions for everything. Due to the global coronavirus pandemic, more people are opting for online payment options. With online payment options, you are also attracting cybersecurity threats to your payment details.
The instances of stealing online payment details and stealing huge amounts of money are not at all new things. Here, you have to ensure that you are using a secured and safe medium for making payments.
6. Personal Data Hacks
Personal data hacks and identity theft are almost similar. Here, cybercriminals can steal your personal data like your identity, email address, password and use those data for evil purposes.
Today we are too exposed to the online world and also unexpected cybersecurity threats. When we are sharing any of our personal data on the internet, we have to be extra careful. However, it is always advised not to share personal data on social media and online platforms.
7. SQL Injection
You might not have heard so much about SQL injection. An SQL injection or structured query language injection is a particular type of cyber attack, where the attackers insert malicious code into a server that is using SQL.
After getting infected, the server starts releasing information. Here, you have to ensure that you are only using those servers, which have extra safety and security.
What is Cybersecurity Threat Intelligence?
Cybersecurity threat intelligence is information gathered, processed, and analyzed to learn about a threat actor’s motivations, targets, and attack patterns. Threat intelligence helps us to make more educated, data-driven security choices and shift from a reactive to a proactive posture in the battle against threat actors.
What Is the Importance of Cybersecurity Threat Intelligence?
Advanced persistent threats (APTs) and defenders are always striving to outmaneuver each other in the field of cybersecurity. Data about a threat actor’s next action is essential for adapting your defenses ahead of time and preventing further attacks.
The following are some of the reasons why threat intelligence is important:
It illuminates the unknown, allowing security professionals to make more informed judgments.
This gives cyber security stakeholders more influence by exposing enemy motivations, strategies, techniques, and processes.
Additionally, cybersecurity intelligence assists security professionals in better understanding the decision-making process of threat actors and allows business stakeholders such as executive boards, CISOs, CIOs, and CTOs to invest intelligently, minimize risk, become more efficient, and make faster choices.
Threat intelligence helps enterprises of all sizes handle threat data so they may better understand their attackers, respond to crises faster, and anticipate a threat actor’s next move. This information enables SMBs to achieve a degree of security that would otherwise be unattainable. Enterprises with huge security teams, on the other hand, can save costs and improve analyst effectiveness by utilizing external threat intelligence.
Be Safe From Cyber Attacks
We hope this article has offered you the necessary information about the most common cyber attacks. In case you still have some queries or doubts, you can always reach us. We will try to come up with a solution as soon as possible.
Till then, be safe online.

Magdalena Polka is a Business Solution Designer and an Information Technology / Project Management consultant and author with over 15 years of software development, management and project management experience.