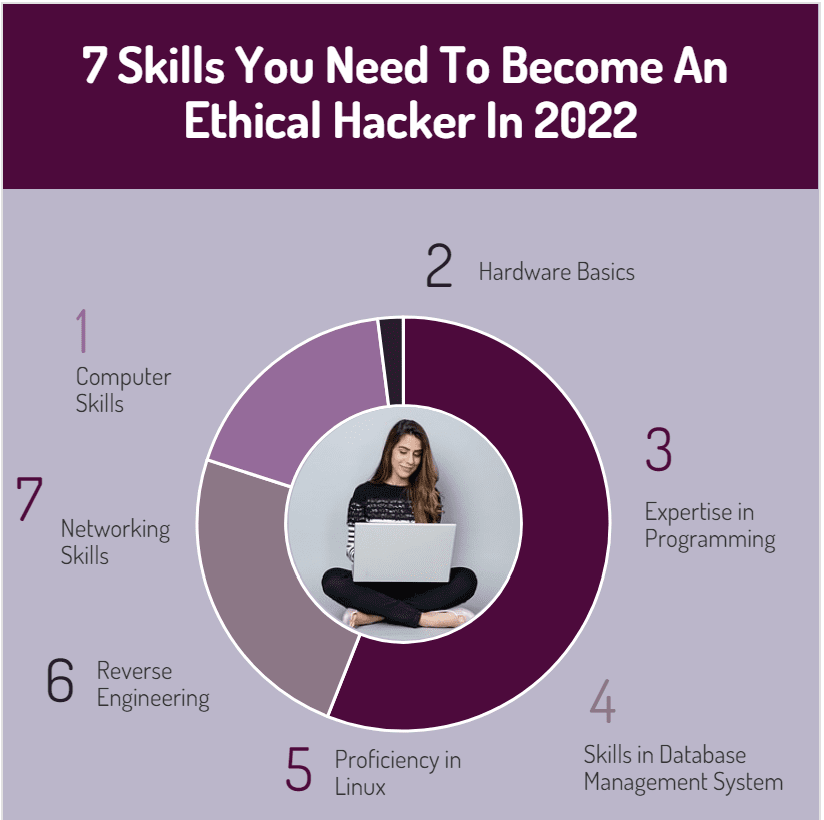
7 Skills You Need To Become An Ethical Hacker In 2022
The pursuit of cyber security has traditionally been referred to as defensive or offensive by usage the terms whitehat and blackhat hacking, respectively. These terms distinguished good guys from bad guys in the cyber world. Despite their common usage, at least one of these terms may be inadequately descriptive of the many roles found in today’s modern cybersecurity ecosystem. A blackhat (malicious) hacker still remains a bad guy, but the good guys are now called red, blue, and purple teams, ethical hackers, and security or network penetration testers as well as certified ethical hacker type. In particular, the red teams provide offensive protection, while the blue teams provide defensive support. Purple mixes blue and red, which indicates teams that cover both areas.
Table of Contents
Ethical Hacking: How to become a certified ethical hacker?
The term ethical hacking refers to the act of compromising a computer system to assess its security and then proactively informing the hacked party. Several job roles in the online security world require ethical hacking skills. The professionals working in these roles keep an organization’s computers, servers, and other items in working condition, preventing unauthorized access through cyberspace.
People believe that “hacking” means penetrating any website within a minute. Since they have learned this concept from watching movies, they do not even know what hacking is or how to do it. Is the goal to crack passwords or steal data? However, the truth is that it goes far beyond that.
An ethical hacker scans for vulnerabilities and looks for possible exploits on a network or computer. It is an ethical hacker’s task to identify weaknesses or loopholes in a computer, web application, or network and report them to the organization.
By doing this, the organization becomes aware of its shortcomings, which can cause them great damage if not addressed timely. In short, ethical hacking is indeed imperative for the future of software engineering as it gives both parties a clear understanding of the loopholes present in their networks and applications.
On this note, let’s look at some of the skills an IT professional needs to possess to become an ethical hacker in 2022.
1. Computer Skills
Computer skill is the knowledge and ability to use computers and related technology. A basic understanding of computers includes data processing, managing computer files, and creating presentations. Database management, programming, and spreadsheet calculations are examples of advanced computer skills.
It is essential to possess skills in MS Office, Spreadsheets, Email, Database Management, Social Media, Web, and Enterprise systems. Ethical hackers must be proficient in computer systems.
2. Hardware Basics
A computer’s hardware consists of the physical components, including the processor, monitor, mouse, input device, hard drive, video card, audio card, speakers, and mainboard. The software is the set of instructions stored and executed by the hardware. Consider, for example, hacking a computer-controlled machine. To do so, they need to understand the machine.
Finally, they need to access the computer that controls the machine. Although the machine will now have a very good software security system, hackers do not care about hardware security, so they can play with it if they can access the hardware. Without knowledge of hardware, you can’t know how the motherboard works, how USBs transfer data, how CMOS or BIOS work together, etc.? Being an ethical hacker also requires some understanding of hardware.
3. Expertise in Programming
Coding skills are also fundamental to becoming an ethical hacker. But what precisely does programming mean in the world of computers? It includes writing code, which can be interpreted by a computational device to perform a variety of instructions. So, to get better at programming, you must write a great deal of code!
Moreover, choosing the right programming language is the first step in writing code. The following list includes the most common programming languages that ethical hackers use.
- Python
- JavaScript
- SQL
- C
- C++
- PHP
- Perl
- Java
- Ruby
4. Skills in Database Management System (DBMS)
The DBMS is the key to creating and managing all databases. Access to a database where all the information is stored can put the company in danger, so it must be hacker-proof. An ethical hacker must understand this and various database engines and schemas to help the organization develop a robust database management system.
5. Proficiency in Linux
Based on the Linux OS kernel, Linux is a community of open-source, Unix-based operating systems. Under the GNU Public License, anyone may modify and distribute the source code commercially or non-commercially.
A certified ethical hacker should learn Linux because it provides better security than any other operating system.
6. Reverse Engineering
By analyzing the code of a product, reverse engineering can determine the product’s design, requirements, and functions. So, through this analysis, information becomes available. A reverse engineering project’s goal is to improve a system’s understandability and produce the necessary documentation to streamline maintenance work.
Reverse engineering is for software security to ensure the system is free of any major security flaws or vulnerabilities. As a result, a system is more robust and is, therefore, less likely to be attacked by hackers and spyware. As a last resort, some developers hack their own systems in order to identify vulnerabilities – an approach known as ethical hacking.
7. Networking Skills
To become an ethical hacker, you need networking skills. A computer network is nothing more than a collection of hosts connected through multiple paths to send and receive data. Besides understanding DHCP, Supernetting, Subnetting, and more, ethical hackers will be able to comprehend the various interconnected computers within a network, along with any potential threats they may pose.
The Takeaway to Become an Ethical Hacker
To sum it all up, the path to becoming a certified ethical hacker isn’t set in stone. Depending on the company’s requirements, they create a job description and look for relevant skills in candidates. Still, if you want to pursue a career as an ethical hacker, you need a degree in computer science, IT, or mathematics. Additionally, if you develop the skills mentioned above, the chances of landing a job in the ethical hacking field will further increase.

Adhar Dhaval is experienced portfolio, program and project leader with demonstrated leadership in all phases of sales and service delivery of diverse technology solutions. He is a speaker sharing advice and industry perspective on emerging best practices in project leadership, program management, leadership and strategy. He is working for the Chair Leadership Co.










I never believed it was possible to recover lost cryptocurrency until few days ago I lost $10.000 to an online purchase scam, I was so sad because I wouldn’t afford to purchase another and then my step mom introduced me to this guy that helped me recover the full amount, I was shocked and didn’t even know it was possible. You can contact him through ([email protected]) or Whatsapp (+46 76 955 12 43 ). and he also helps with bad credit increase and can also help you gain access into locked phones and computers.
Many have mistakenly lost their bloody difficult money through binary option trading, but instead of going to real hackers who can help them recover it, they go meet bogus hackers who are also con artists. As a result, they wind up losing additional money. After being promised your fortune by the binary firms, I can comprehend how terrible it is to be a victim of a binary option trading scam and have them ignore you in order to cut off communication and steal from you. I’m doing everything I can to help those innocent folks who were harmed by informing them about computer speciallist recovery. A specialist group of hackers called computer speciallist Recovery helps users in recovering their lost or stolen bitcoins. I’m mentioning this because I was a victim as well, and computer speciallist Recovery helped me survive by supporting me in getting back my looted bitcoins. To anyone who has lost money in a currency scam, I’d heartily suggest them.