Employee Central SAP Success Factors and its connection with Access Request & Risk Analysis in SAP GRC
This post will explain Employee Central System Success Factors, GRC, How to set up and permit the SAP Success Factors and Access Control integration for Access Risk Analysis and Access Request, Risk Analysis of Access in the Success Factors GRC System, Request for access to the GRC System’s Success Factors. You have to master GRC by accrediting the online certification program on the SAP GRC Training course. The course enables you to learn the concepts such as Access control with GRC, risk assessment, and mitigation, super users privilege management, Provisioning of compliant users, the role of enterprise management, etc.
Table of Contents

Employee Central & Risk Analysis for SAP GRC Integration as Success Factors
The following are the five major success factors that are considered for Employee central with SAP GRC.
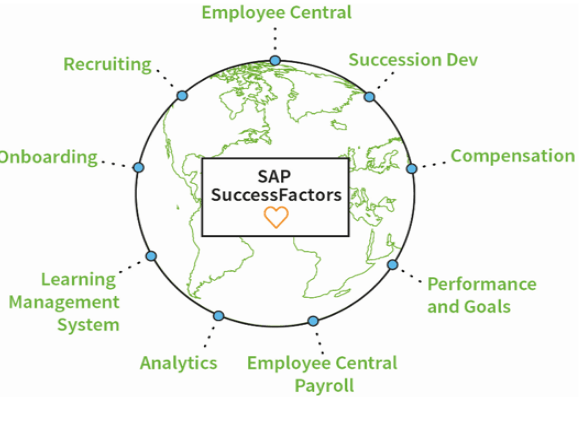
1. What are the SAP Success Factors for Employee Central?
“SAP Employee Central’s SuccessFactors is an HR solution based on cloud that consolidates all the data of an employee into one platform to provide small and medium-sized organizations with improved perspective into their employees”.

The Success Factors of SAP is an HCM system based on a cloud built on the SaaS concept. Before going further, you can get a certificate for this online success factors course and learn the essential skills needed to understand the success factors. Employee Central from Success Factors allows you to handle core HR processes and includes the data of HR master such as employee name, identity, and user name.
The following are the most crucial Employee Central features:
- Although SuccessFactors service is based on the cloud that is managed quarterly, users can quickly adapt to changing workforce structures.
- Employee central SuccessFactors keep track of many events that occur during an employee’s career. Employee Central allows users to keep track of basic events such as new hires, promotions, transfers, and new assignments, as well as additional activities.
- SuccessFactors Employee Central’s ERP integration is much more robust, resulting in an HR solution of greater quality.
2. SAP Success Factors Key Features
The SAP Success Factors HCM solution based on the cloud includes the following important features.
- Transfers and Changes
- HR Transactions
- Recruitment
- Overview of Performance
- Time Off
- Position Management
- Extensibility & Integration
- Auditing, Compliance, and Reporting
- Timesheets for Payroll
- Training and development
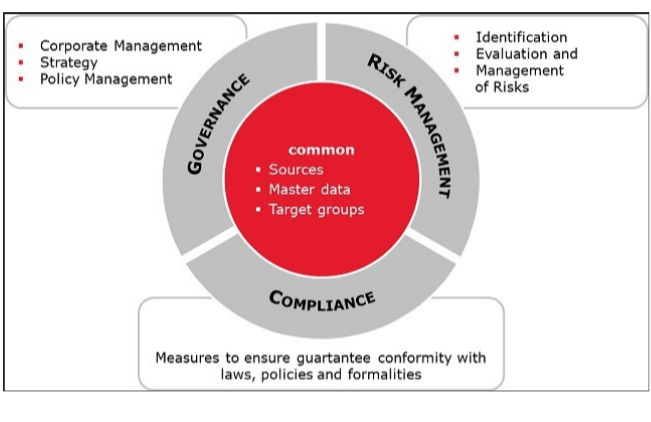
3. Governance, Risk, Management
GRC system is a management strategy for an organization’s overall GRC, and regulatory compliance. GRC is an integrated set of abilities that enables an enterprise to maintain cyber security while also protecting its data. Information availability, Integrity, and Confidentiality are provided by the GRC system.
“Confidentiality is a set of regulations that restricts who has access to certain types of information; Integrity is a promise for the reliable and correct information, and availability is the assurance that authorized people will have reliable information access”.
Example:
“There are two roles in your company: one is to hire the employees and the other is paying them a salary. Assuming that hiring and paying wages to the same worker is a risk and that any worker in the organization has these roles, this can lead to fraud. However, via GRC, we could identify risks, mitigate them, and manage them so that they do not impact the company.”
4. The Essential Factors of Success Employee Centralization and GRC Controlled Access Integration
“Customers in SAP Success Factors Employee Central HCM were unable to handle access requests, provision Success Factors users, establish systems that permit them to recognize and minimize risk while guaranteeing compliance (This necessitates an examination of how you control and how you carry out your duties), and analyze risks of critical access and SOD for users.”
“Customers may utilize Access Control for monitoring access requests, evaluate Access Risks with Critical Permissions, Critical Action, SOD, provision SuccessFactors users, and Critical Roles due to this integration.”
“Customers may better handle compliance and risk, improve cybersecurity, identify and prohibit fraud, and optimize the controls as a result of this.”
“From a risk management standpoint, It makes a lot of sense to integrate SAP GRC and SAP HCM. Within the HR process itself, there is a variety of SOD and risks of sensitive access that must be carefully handled – just like any other risk of access.”
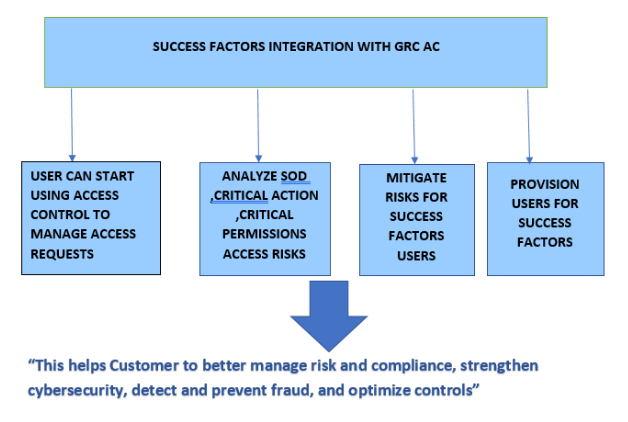
5. SAP Success Factors integration with Access Controlling at a high level
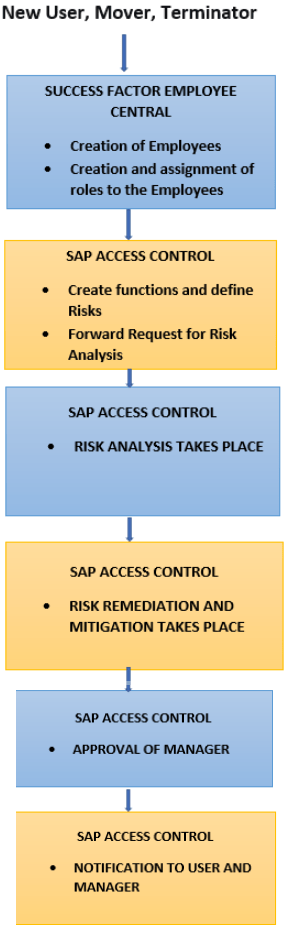
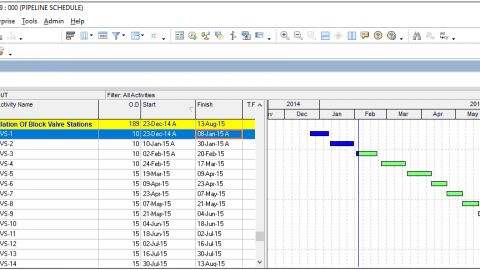
The below picture illustrates the steps to be implemented for Access Control Integration.
Steps for configuring and enabling the Controlling Access and Accessibility Success Factors Integration of access-requests and risk analysis
The process from configuring the system connectors to finishing the synchronization among the two systems is depicted in the configuration below. After the setups below, users would be capable of handling Success Factors Provisioning, risk analysis, and access requests in Access Control.
The below Access Control abilities must be integrated with Success Factors by the user.
- Role Management
- Risk Analysis of Access
- Management of Access Requests
To permit the integration between Access Control and Risk Analysis of Access and Access-Request Success Factors, the user must complete the following Integration Scenarios.
- 0001 Generating Role
- 0002 Risk Analysis by Role
- 0004 Provision
Methodology for Handling Risks
Violations or risks could be solved by either fixing the risks or mitigating them through control assignment.
The Best Approach to Risk Remediation
Before attempting to mitigate risk, the user should always seek to fix it. The approach for eliminating risks in roles is determined during the risk remediation phase. The remediation phase’s goal is to figure out what other options there are for resolving problems. Remediation is the process of removing risks from a system without relying on mitigation controls.
Instead of implementing mitigation controls, users should always look for a solution to remedy a risk, as mitigation might lead to unethical activities.
Mitigating Risk
If the user is unable to eliminate the risk, he or she should consider mitigation. We assign the mitigation to lessen the risk’s impact. The user must create a risk mitigation control. Approver and Monitor should be included in the mitigation control as well.
Request for Self, Other User, and Roles Assignment/Static Groups to Users for GRC Success Factors
On the Access-Request Screen, a user can create access requests for himself, another user, or multiple users.
- Navigate to -> NWBC -> Access Management -> Access Request.
- Choose a Request Type (example -Change Account), Request for (example-Self).
- If you wish to assign roles to employees, go to the bottom of the table and click “Add” and then “Select Roles.” The Select Roles window will pop up.
- Fill in all of the required parameters, such as Role Name, Role Type, and System, and then click Search.
- Roles will appear in the table below based on your search parameters; select the role that you would like to request for your employee.
Conclusion
We may perform the risk analysis and create access requests for Success Factors in the GRC system, as well as configure and enable the interaction between GRC and Success Factors, by following all of the preceding procedures. In this blog, We have learned all the prerequisites of GRC and Success Factors briefly.
Karna Jyoshna, Post graduate in Marketing, Digital Marketing professional at HKR Trainings.
I aspire to learn new things to grow professionally. My articles focus on the latest programming courses and E-Commerce trends.




SAP is very useful for the HR transactions,Reportings and Auditing
If anybody want to learn the snowflake masters and appian training once visit to our training institute, we trained by the experts and 100% placement guaranteed.
SAP is very useful for the HR transactions,Reportings and Auditing
and follw my url and get the link so nise you are blog
Java Full Stack development is a powerful and sought-after skillset in the realm of web development. The ability to create end-to-end solutions using Java empowers developers to build robust, scalable, and efficient web applications. As organizations increasingly embrace full-stack development, mastering Java Full Stack opens up exciting career prospects and ensures the capability to contribute effectively to the ever-evolving landscape of web development.
I have seen good contents Nice informative blog.
Thanks for sharing.
I have seen good contents Nice informative blog.
Thanks for sharing.