Remote Administration Tools: Revolutionizing Network Management
In today’s interconnected world, network management has become a critical aspect of businesses and organizations across various industries. The efficient management and administration of computer networks are vital for ensuring smooth operations, maximizing productivity, and safeguarding sensitive information. With the rapid advancements in technology, the emergence of remote administration tools (RATs) has revolutionized the way network management is conducted, bringing unprecedented convenience and efficiency to administrators and IT professionals. This article explores the significance of remote administration tools in network management, their benefits, and their impact on the modern business landscape.
Table of Contents
Remote administration tools refer to a set of software applications that enable administrators to manage and control computer systems and networks from a remote location. Traditionally, network administrators had to be physically present at the location of the network infrastructure to perform various tasks such as system monitoring, troubleshooting, software installations, and updates. This approach was time-consuming, expensive, and limited in terms of scalability. However, with the advent of remote administration tools, administrators can now perform these tasks from anywhere in the world, as long as they have a secure internet connection.
Ability to enhance productivity and efficiency with Remote Administration Tools
By eliminating the need for physical presence, administrators can now manage multiple networks and systems simultaneously, saving valuable time and resources. They can remotely access servers, workstations, and other network devices, troubleshoot issues, apply updates, and configure settings with just a few clicks. This level of convenience not only streamlines network management processes but also enables administrators to respond promptly to any network emergencies or security threats, minimizing downtime and ensuring continuous operations.
Empower organizations with geographically distributed infrastructure
Companies with branch offices or remote workforce can leverage these tools to efficiently manage their network resources. Administrators can remotely deploy software updates, enforce security policies, and monitor network performance across multiple locations, all from a centralized console. This centralized approach to network management enhances consistency, reduces operational costs, and enables organizations to scale their operations seamlessly.
Contribution to enhanced security and risk mitigation
By providing administrators with remote access to critical systems and devices, these tools enable proactive monitoring and rapid response to potential security breaches. Administrators can monitor network traffic, detect suspicious activities, and apply security patches in real-time, thus reducing the vulnerability window. Additionally, remote administration tools often employ robust authentication and encryption mechanisms to ensure secure communication between administrators and network devices. Hence, safeguarding sensitive data from unauthorized access.
Disaster recovery and business continuity planning
In the event of a network failure or a natural disaster, administrators can remotely access backup systems, restore data, and initiate recovery procedures without the need for physical intervention. This capability ensures minimal downtime and enables businesses to quickly resume their operations, preventing significant financial losses and reputation damage.
Remote administration tools are not without their challenges and considerations
As with any technology that involves remote access, security is a primary concern. Organizations must implement robust security measures, such as strong authentication, encryption, and access controls, to prevent unauthorized access to their network resources. Additionally, organizations must ensure that their administrators are adequately trained in using these tools. And adhere to best practices to minimize the risk of human errors or misuse.
- Use reputable and trusted RATs from reliable sources.
- Regularly update and patch RAT software to address vulnerabilities.
- Implement strong access controls and authentication mechanisms.
- Employ firewalls, intrusion detection systems, and antivirus software to detect and prevent unauthorized access or malware propagation.

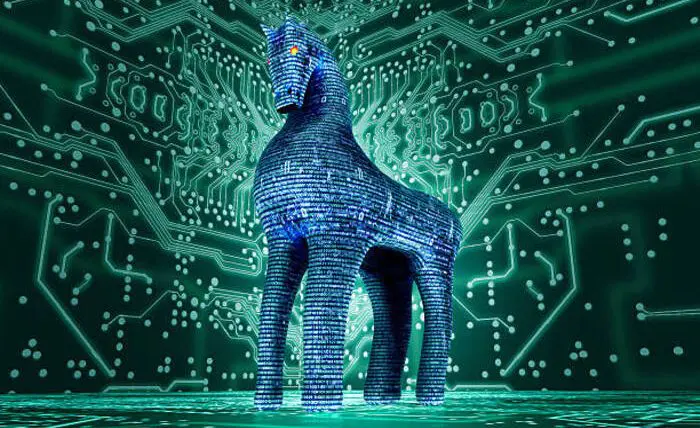
What is the difference between a RAT and a Trojan?
A Remote Access Trojan (RAT) and a Trojan are both malicious software programs designed to gain unauthorized access to a computer system. While they share similarities, there are key differences between the two.
A RAT- remote administration tools- is a type of malware that allows an attacker to control a target computer remotely. Once a RAT is installed on a victim’s system, the attacker gains full control over the infected device, enabling them to perform various malicious activities. This includes stealing sensitive information, monitoring user activities, recording keystrokes, activating webcams, and even executing commands. RATs often operate stealthily and are commonly spread through email attachments, malicious websites, or software vulnerabilities.
On the other hand, a Trojan, or Trojan horse, is a broader category of malware that disguises itself as legitimate software or files to trick users into executing or downloading them. Trojans do not provide direct remote access to the attacker. But instead create a backdoor in the system for unauthorized access. They can perform a range of malicious actions. Such as stealing personal information, deleting files, modifying system configurations, or facilitating the installation of other malware.
Conclusion on Remote Administration Tools
Remote administration tools have revolutionized network management by providing administrators with the ability to control and manage networks from remote locations. Their benefits, such as enhanced productivity, scalability, improved security, and disaster recovery capabilities. Hence, these make them indispensable in the modern business landscape. As technology continues to advance, remote administration tools are expected to evolve further. They are offering even more sophisticated features and capabilities to meet the growing demands of network management. The use of RATs must comply with applicable laws and regulations. It is essential to understand the legal implications and obtain appropriate consent before deploying RATs on systems or networks.
Ethical considerations are crucial when using RATs. Unauthorized or intrusive use of RATs can violate privacy rights and ethical boundaries. It is important to use RATs responsibly and only for authorized purposes. Organizations and individuals must implement robust security measures, adhere to legal requirements, and use RATs ethically to ensure the protection of systems, data, and privacy.

Ananya Prisha is an enterprise level Agile coach working out of Hyderabad (India) and also founder of High Level PM Consultancy. Her goal has been to keep on learning and at the same time give back to the community that has given her so much.